In today's interconnected world, leveraging IoT devices remotely has become essential for many professionals. However, navigating through firewalls to access RemoteIoT on a Mac can seem daunting, especially when you're unsure of the steps involved. This comprehensive guide will walk you through how to use RemoteIoT behind a firewall on Mac without unnecessary complications.
Whether you're a network administrator, developer, or tech enthusiast, this article is designed to provide practical and actionable insights. By the end, you'll have a clear understanding of how to configure and manage your Mac for seamless RemoteIoT access, even behind restrictive firewalls.
Our focus is on delivering a step-by-step guide that addresses common challenges and offers solutions to help you achieve a secure and efficient setup. Let's dive in and explore the possibilities of RemoteIoT on your Mac.
Read also:Luxmovies New Link Your Ultimate Guide To Streaming Movies Online
Table of Contents
- Understanding RemoteIoT Basics
- What Is a Firewall and Why It Matters
- Mac Setup for RemoteIoT
- Port Forwarding Explained
- Using a VPN to Access RemoteIoT
- Essential Tools for RemoteIoT Access
- Security Best Practices
- Troubleshooting Common Issues
- Alternative Solutions
- Conclusion
Understanding RemoteIoT Basics
What is RemoteIoT?
RemoteIoT refers to the ability to control and monitor IoT devices remotely, typically over the internet. It allows users to interact with smart devices from anywhere, enhancing productivity and convenience. Understanding its core functionality is crucial before attempting to configure it behind a firewall.
Why Use RemoteIoT?
There are several compelling reasons to use RemoteIoT:
- Enhanced accessibility to IoT devices
- Improved efficiency in managing smart systems
- Cost savings by reducing the need for on-site visits
What Is a Firewall and Why It Matters
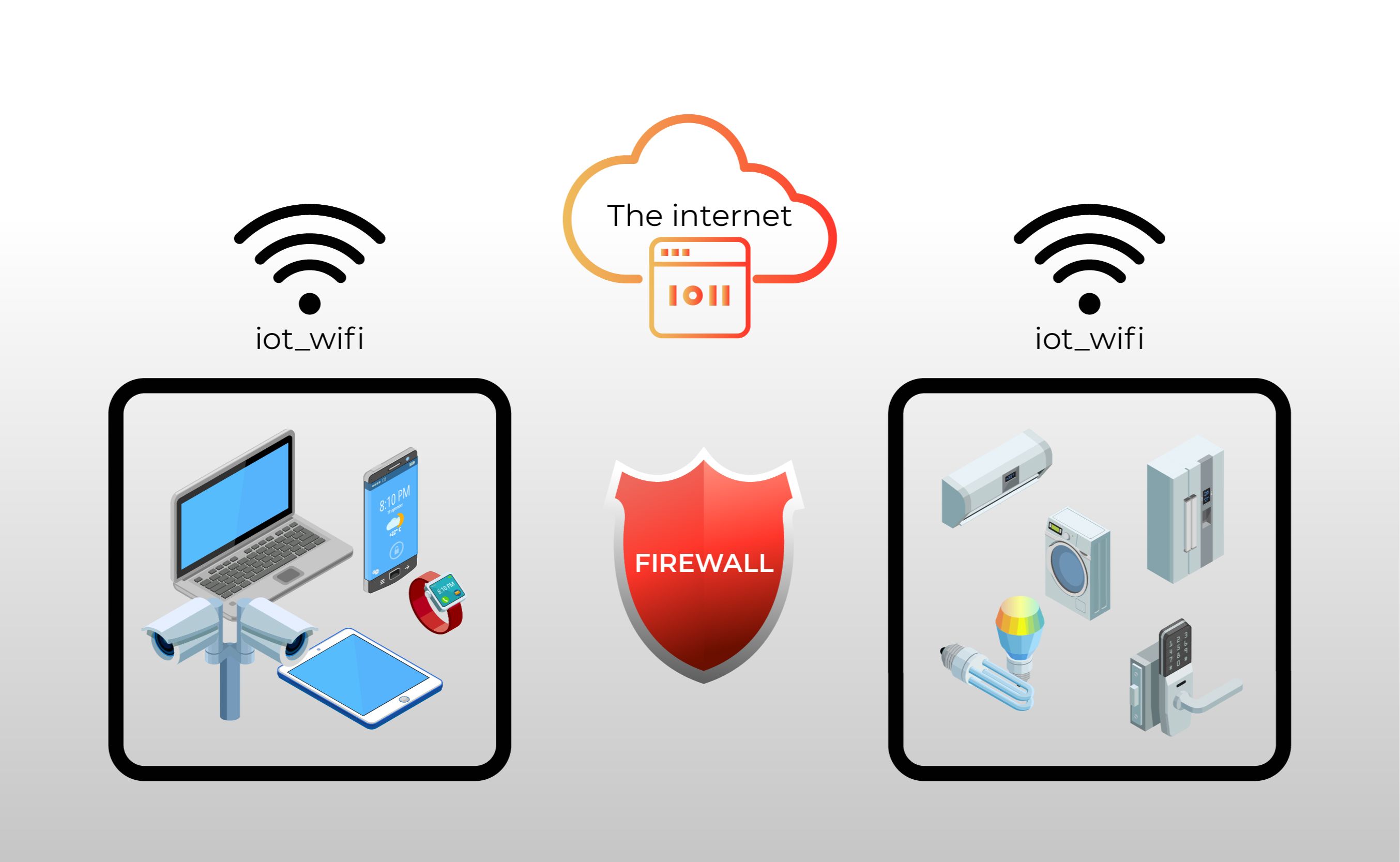
A firewall is a security system that monitors and controls incoming and outgoing network traffic based on predetermined security rules. When using RemoteIoT behind a firewall, understanding its role is essential to ensure smooth communication between your Mac and IoT devices.
Types of Firewalls
Firewalls come in various forms, including:
- Software firewalls
- Hardware firewalls
- Cloud-based firewalls
Mac Setup for RemoteIoT
Configuring your Mac for RemoteIoT involves several key steps. Below, we'll outline the process to help you set up your system effectively.
Step 1: Update macOS
Ensure your Mac is running the latest version of macOS. Updates often include security patches and improvements that can enhance compatibility with RemoteIoT applications.
Read also:5 Movierulz Kannada 2023 Unveiling The Latest Movie Releases And Trends
Step 2: Install Required Software
Depending on your RemoteIoT setup, you may need to install specific software or drivers. Refer to the official documentation for your chosen platform to identify necessary installations.
Port Forwarding Explained
Port forwarding is a technique that allows external devices to access services on a private network. When using RemoteIoT behind a firewall, configuring port forwarding on your router can be a viable solution.
How to Set Up Port Forwarding
- Log in to your router's admin panel
- Locate the port forwarding settings
- Specify the internal IP address and desired port numbers
Using a VPN to Access RemoteIoT
A Virtual Private Network (VPN) can provide a secure tunnel for accessing RemoteIoT behind a firewall. By encrypting your connection, a VPN ensures that your data remains protected while bypassing firewall restrictions.
Choosing the Right VPN
Consider the following factors when selecting a VPN:
- Security features
- Speed and reliability
- Compatibility with macOS
Essential Tools for RemoteIoT Access
Several tools can facilitate RemoteIoT access behind a firewall. Below are some of the most effective options:
SSH Tunneling
Secure Shell (SSH) tunneling creates an encrypted connection between your Mac and the RemoteIoT server, allowing you to bypass firewall restrictions securely.
Dynamic DNS Services
Dynamic DNS services help maintain a stable connection by updating your IP address automatically, ensuring consistent access to your RemoteIoT devices.
Security Best Practices
When accessing RemoteIoT behind a firewall, prioritizing security is paramount. Follow these best practices to protect your system and data:
- Use strong, unique passwords
- Enable two-factor authentication (2FA)
- Regularly update software and firmware
Troubleshooting Common Issues
Even with proper configuration, issues may arise. Here are some common problems and their solutions:
Connection Refused
If you encounter a "connection refused" error, verify that the required ports are open and accessible. Double-check your firewall settings and ensure that no conflicting rules are in place.
Slow Performance
Slow performance can be caused by network congestion or insufficient bandwidth. Optimize your network settings and consider upgrading your internet plan if necessary.
Alternative Solutions
While the methods discussed above are effective, alternative solutions may better suit your needs. Consider the following options:
Cloud-Based Platforms
Cloud-based platforms offer a scalable and secure way to access RemoteIoT devices without the need for complex configurations. Many providers offer robust security features and user-friendly interfaces.
Third-Party Applications
Several third-party applications specialize in remote access solutions. Research and evaluate these options to find the best fit for your requirements.
Conclusion
In conclusion, using RemoteIoT behind a firewall on a Mac is achievable with the right approach and tools. By following the steps outlined in this guide, you can ensure a secure and efficient setup. Remember to prioritize security and stay informed about the latest advancements in remote access technology.
We encourage you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our site for more insightful content. Together, let's continue learning and growing in the world of technology!
Data Sources: